Yes, it has been a long time since we had a social engineering poll. But we are ready to release the results of one of the most successful so far, as well as start a new poll.
Endearment vs Authority
This poll as based on two different stories. The first showed how the principle of endearment may be used by a malicious social engineer.
The second story involved a social engineer employing the authority principle. By simply carrying a clipboard and acting in charge could a social engineer manipulate people into giving up valuable data?
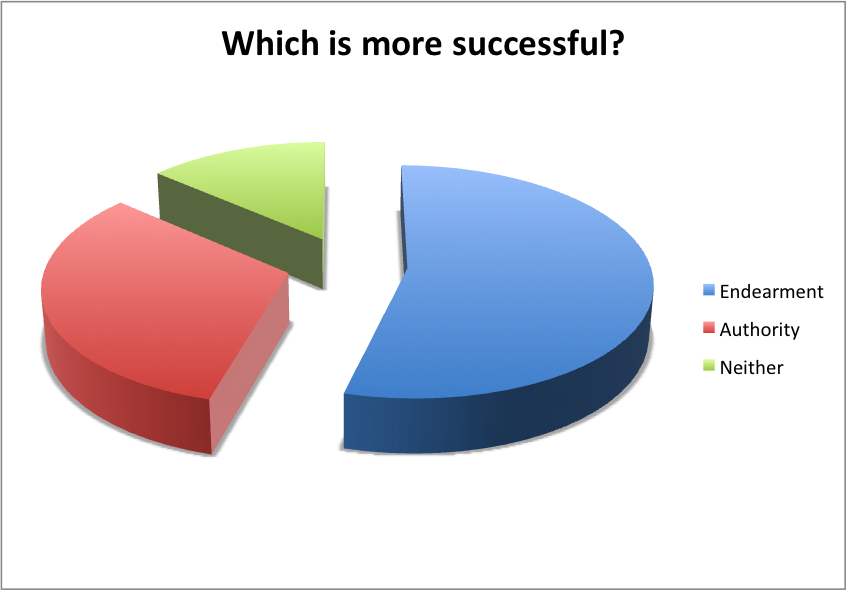
These two scenarios were presented with a third option that neither of them would work. How did the results turn out?
We allowed for a long period of time to collect as much data as possible. The only thing we asked for was Gender, Field Worked In and their choice. The statistics can give us some insight into not only which is more popular but also which is more popular based on the gender.
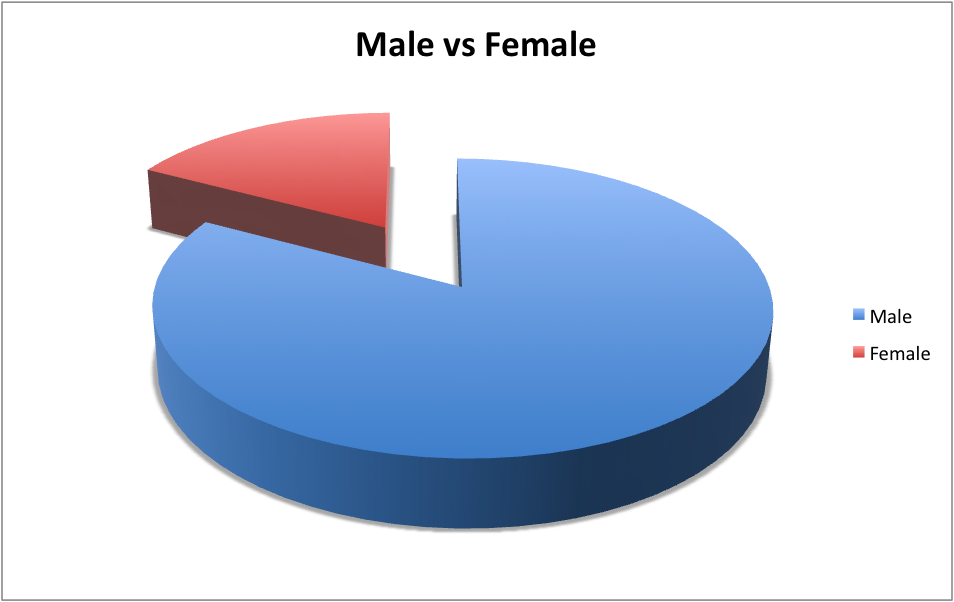
Our first data set is the most simplistic and sets a baseline for the poll, Gender.
Again, as in most of our polls there was substantially more males than females participating. (Yes we need to find a way to motivate you ladies to vote… we think we have it in this months Social Engineering Poll) Although this doesn’t necessarily skew the results that there is more males, what we find interesting is how the results came out knowing there is more males.
Endearment seemed to take the largest portion of chosen methods they felt would work. Endearment is defined as “a term or act expressing affection.” We would have guessed that most would have chosen authority, but in fact we agree that endearment works in more cases over authority. A simple word or action that can make someone feel you care can go a long way into building rapport, trust and a relationship that will cause that person to want to give you the information you seek.
Even though we feel that way and it seems the large majority of people as a whole feel that way, we wanted to see if the results would be the same with in the same gender.
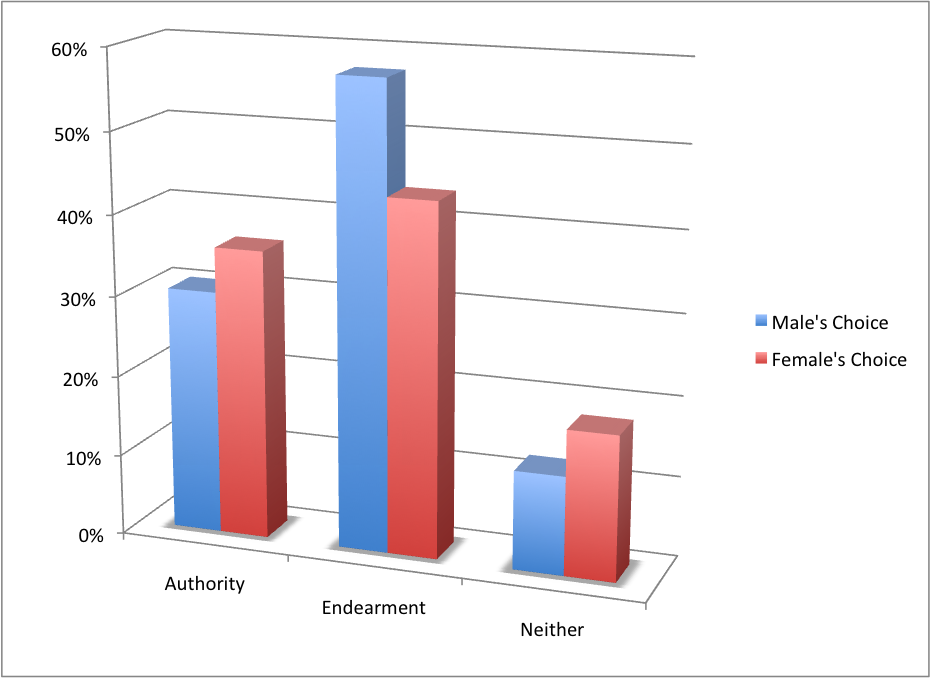
Endearment still took first place in both men and women as the method they felt would be the most effective technique. Authority was much further behind with the males, which we found interesting too.
Why? Humans are naturally trusting creatures. We want to help those in need, we want to believe there is good in all people, we want to provide answers to those doing the asking. Not only that but we do all of this with more emphasis and zeal for those we consider our friends. So a social engineer that can endear themselves to us can create an environment that will make it next to impossible to say “no” to any request.
It is that trusting attitude that has lead many to unfortunately being hacked. What can you do?
We are not saying to not be trusting, but just to become a critical thinker. The requests that are being laid upon you, the questions being asked – do they make sense? Is it really needed to answer those questions to this individual? Critical thinking can go a long way. Secondly, get educated. Be aware of the attack vectors that are being used and learn how they are being facilitated. That can keep you aware.
Now get over to our new social engineering poll and vote.


Comments are closed.