Information Security: How Well is it Being Used to Protect Our Children at School?
August and September are ordinary months to some, but to others they are a time of mixed emotions. It’s the start of another school year. Some are sad to see their children off, while others celebrate that day. The start of the school year brings with it a lot of paperwork and sharing of sensitive information. How well is information security being used to protect our children’s information, and even the school staff’s, personally identifiable information (PII)? How well is it being used to protect against social engineering attacks?
Think about the information that the schools keep; when you registered your child, you may have had to give them copies of their birth certificate, social security number, your phone number, and other personal information. You may have had to give your own social security number, especially if you had to fill out an application for free and reduced-price meals, or you had to register to volunteer at the school. If your child is in a college or university, even more information has to be given such as financial records, medical records, and high school transcripts. What is being done to keep that information secure?
When I read the following headlines they make me a little concerned, how about you?
- Magicvalley.com reports: Nearly six weeks after being hit by a massive ransomware cyberattack, the Jerome School District is still working to recover
- The State of Security reports: School District to Spend $314K on Rebuilding Servers after Malware Attack
- HIPAA Journal reports: UCLA Health System Hacked: 4.5 Million Patient Records Exposed
- BBC News reports: Top university under ‘ransomware’ cyber-attack
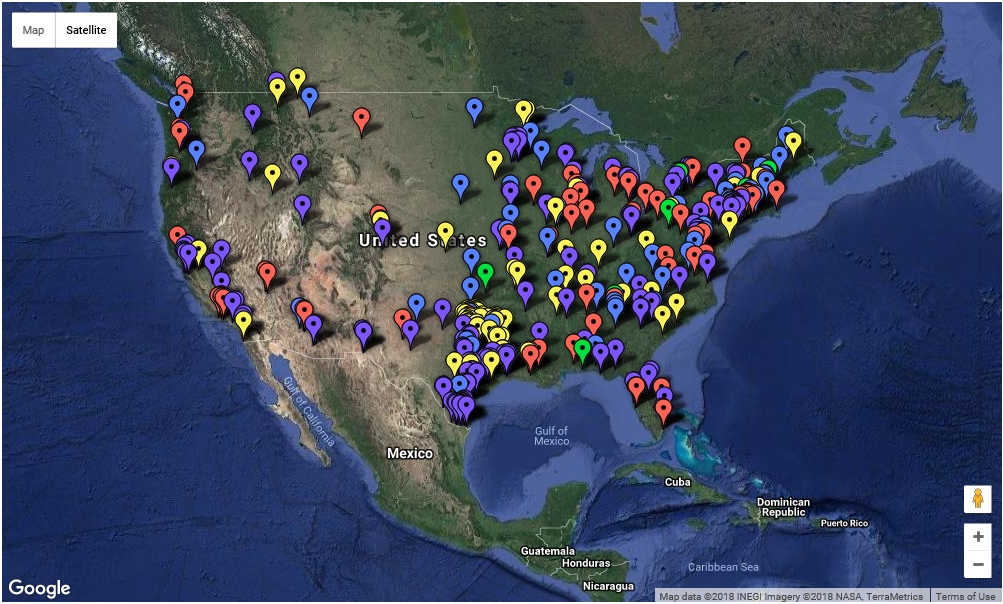
These are only a few of the many stories out there. According to the Breach Level Index by Gemalto, the education sector had 33.4 million records breached in 2017 and a total of 199 reported breaches. This is a 20% increase of reported incidents over 2016. It gives meaning as to how widespread the incidents are when I see it visually on the K-12 Cyber Incident Map by the K-12 Cybersecurity Resource Center.
Who are Breaching School Networks and Why are They Doing it?
Who are trying to breach a school’s network? It’s not just the student doing it to change grades or for fun, it’s also the elite attacker and the common cybercriminal. Thanks to the ease of availability of hacking tools, and the sharing of malicious attack techniques on the dark web, they are able to install ransomware, encrypt drives, and demand payment to decrypt them. They are also able to exfiltrate PII and passwords to gain further access to networks and steal and create identities. Identity thieves will use the child’s information to create their own false identity where they can take out credit cards and loans, ruining your child’s credit. When this happens, it can make it difficult to get a license, go to college, or get any loans.
How are They Doing it?
Cybercriminals are opportunists who will take advantage of any vulnerabilities, especially with organizations that are less secure. Unfortunately for educational institutions, their security stance is usually poor and at a high risk. They battle staffing and budgetary constraints, their view of cybersecurity has been one of a low priority, and they view security as an inconvenience.
Another point of weakness is the ease of accessibility to the school’s network. They usually have free Wi-fi, large numbers of desktop and mobile devices, and weak passwords which all present potential points of entry into the network. In addition, students will browse the web from insecure networks and often pick up malware which can then be inadvertently shared with others via email or uploads of coursework to the secure school network.
So, what do cybercriminals do? They use a variety of web- and email-based attacks that are at their disposal. One web-based attack is that they actively target sites where students will commonly browse. These are often completely legitimate sites, such as Thesaurus.com. No click required; just viewing the ad can initiate the malware download.
An example of an email-based (phishing) attack targeting education was at Northeastern University, where some Blackboard Learning users were targeted by an email that tried to influence the reader into clicking a link that was disguised to be legitimate and tried to compel the action by using a time constraint.
With web- and email-based attacks, the cybercriminal can deliver ransomware and steal student records. All at a great cost to the school system and to those that have their information compromised.
What Can be Done?
When it comes to protecting our children we are willing to do anything, so what can we do to protect our children’s information?
Here are some things that parents can do:
1. Make sure that the personal computer that is used to log into the school’s network is up-to-date;
2. Make sure that computer has more than just an antivirus installed, add malware protection as well;
3. Be proactive and educate yourself and your children on security awareness;
- Read the Social Engineer Framework;
- Have your child create usernames that don’t contain personal information, such as birth year;
- Look at using a private VPN when on an insecure network, such as at Starbucks. Trustworthy VPNs will usually have a fee for using them;
- Teach children the importance of not giving out information;
- Use a secure password manager and don’t share passwords;
- Make sure teens don’t take a picture of their license and share it on social media; and
- Don’t throw important documents in the trash, shred them.
4. Be watchful of your student’s browsing activity; and
5. Something you may wish to look into is an identity theft protection service to protect your child against identity theft.
Remember that just because you are asked to give out information doesn’t mean you have to. Ask, “why is it necessary for them to have that information?”
Schools need to follow the industry best practice in information security and we, as parents, need to demand that it be done. Schools should also be forced to address the human element in security:
- Staff, teachers, students, and parents need to be educated and used as a line of defense; and
- Institute security awareness training which includes: Performing simulated phishing exercises; Recruiting on-campus security advocates; and Holding onsite security education activities, lectures, and in-class training.
Following these suggestions will help to protect our children’s information at school.
Need Inspiration?
If you want some inspiration, look at what some schools are doing:
- One example is that the July 2017 article of The Educator in San Diego, CA said that, “the local ESET office runs an annual cyber boot camp for about 50 middle and high school students.”
- Another example was in the June 2017 article of The Educator, where it discusses how the Macquarie University in Australia uses the BlackBerry AtHoc as part of the University’s Emergency Management Plan and that the system will assist the school in managing and mitigating social engineering incidents, for example, by sending a message to staff and students recommending not to open a certain email or click on a certain link.
To some, the suggestions may be easier said than done, but, if they aren’t followed, the school nearest you may be the next cybersecurity incident we read about. Information security must be implemented to protect the sensitive information (PII) that is housed at the schools, especially that of protecting our children’s information.
Stay safe and secure.
Written By: Mike Hadnagy
Sources:
https://www.theeducatoronline.com/au/news/is-your-school-protected-against-cyber-threats/237855
https://www.theeducatoronline.com/au/technology/infrastructure-and-equipment/how-malware-could-be-threatening-your-school/246146
https://edtechmagazine.com/k12/article/2016/04/how-ever-worsening-malware-attacks-threaten-student-datahttps://blogs.cisco.com/education/the-surprisingly-high-cost-of-malware-in-schools-and-how-to-stop-it
https://blog.barkly.com/school-district-malware-cyber-attacks
https://in.pcmag.com/asus-zenpad-s-80-z580ca/124559/news/facebook-serves-up-internet-101-lessons-for-kidshttps://www.stuff.co.nz/business/105950814/schools-promised-better-protection-from-ransomware-as-taranaki-school-blackmailed
https://www.eset.com/int/about/why-eset/

