The COVID-19 pandemic has changed the way we live in many ways. In response to the pandemic, many businesses have implemented remote workforces. As a result, millions of Americans now work from home instead of their place of employment. This rapid shift has increased the vulnerability of many organizations. According to Forbes, Cyber intelligence firm CYFIRMA revealed cyberthreats related to coronavirus shot up 600% from February to March of 2020. Many Corporations are taking extensive measures to protect themselves from cyber-attacks. However, they often overlook the role of social engineering in cybersecurity.
Malicious actors use emotions in human hacking with a high success rate. Indeed, even the most experienced IT professional can be a victim of this type of attack. Hackers use emotions as a social engineering tool, to persuade their victims to take an action they normally would not. The best way to protect yourself from these attacks is by becoming familiar with the techniques used. Bad actors manipulate the following four emotions the most in social engineering attacks.
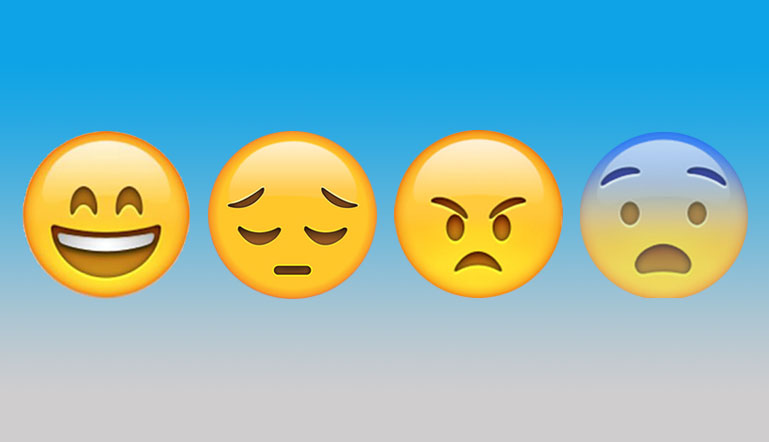
Fear
Malicious actors commonly use fear to manipulate their victims because it is one of the most powerful human emotions. For example, a phony email stating that your online bank account has been compromised and requires a new password will elicit fear in most people. In addition, the emotion of fear can be elicited by a phony email stating that your online bank account has been compromised and requires the password. A much more fearful attack would include a “virtual kidnapping” scam, in which the victim is told that a loved one has been kidnapped and, through deceptions and threats, victims are coerced to pay a ransom before the scheme falls apart. For victims of these attacks, acting in fear results in a negative outcome.
Greed
Greed is a selfish and excessive desire for more of something (such as money) than a person needs. Most of us have fell victim to greed at some point. Greed is part of being human and for this reason, social engineers find it to be a very successful tool. A very good example of this is the “419 Nigerian scam,” in which cybercriminals claiming to be a Nigerian official or agency via phone or email would promise a large reward for a small sum of money. Eventually, the target would share their bank account information in order to receive the reward.
Helpfulness
From a young age, most of us are taught to be helpful and obedient in order to be perceived as a good person. Being helpful can be an asset on many occasions, however willingness to help others can be used against a person during malicious social engineering attacks For example, criminals seek out customer service agents because their “helpful” mindset makes them easy targets. Attackers will encourage them to divulge or confirm more information than they should.
Curiosity
Curiosity is another technique used in social engineering. The attackers promise something of interest or advantageous to deceive the victims. This type of attack could be as simple as sending an email stating “Your Amazon purchase for the amount of $800.00 is ready to ship. Click here to view your order.” This type of email may trigger the curiosity of the target, who may feel compelled to click on the link.
Protect Yourself
How can you protect yourself and your business from a social engineering attack? Knowledge is power. Whether as an individual or corporation, staying up to date regarding these types of attacks, will create awareness and help to avoid falling victim to them. Below are some helpful tips to help prevent a social engineering attack.
- Install and maintain anti-virus software, firewalls, and email filters.
- Never open emails whose senders you do not know.
- Do not open attachments in emails of unknown origin or click on their links.
- Do not provide personal information or information about your organization, unless you verify a person’s authority to have the information.
One of the best social engineering tactics is to keep you from thinking critically, usually by targeting emotion. The most powerful weapon against social engineering attacks is critical thinking. Given the emotional nature of these attacks, there may not be a specific tool or process that can prevent us from falling victim to human vulnerability. Being aware of such vulnerability, enables you to pause and think of the request. Ask yourself, is this request reasonable? Why are they asking this of me? Should I do this?
At times, a social engineering attack can sound “reasonable;” you should still give yourself time to pause. Take a few minutes to let your emotions cool off before taking action. Holocaust survivor Victor Frankl once said, “Between stimulus and response, man has the freedom to choose.” Remember that the goal of a social engineering attack is to use your emotions against you to elicit a reaction based on your emotional state. As you pause and allow space between “stimulus and response,” you can empower yourself to choose wisely.
Learn More About Emotions and Human Hacking
As many corporations and individuals are becoming more aware of social engineering, they are looking for ways to protect themselves. One way to do this is by learning as much as possible about the tactics that malicious actors use, as well as implementing best security practices.
The Human Hacking Conference (HHC) is “an all-encompassing event that teaches business, security, technology, and psychology professionals the latest expert techniques in human deception, body language analysis, cognitive agility, intelligence research, and security best practices.” Whether you want to protect yourself against social engineering attacks or become an expert in spotting deception, the HHC brings together world-class lecturers to provide the most cutting-edge educational experience to learn the advanced art and science of “social engineering. The Human Hacking Conference is happening March 11-13, 2021. Learn how you can be a part of it by visiting https://www.humanhackingconference.com/. Still on the fence about attending? We just added day tickets, giving you the option of attending whatever day you want and choosing your preferred workshops! Just select your day when registering.
Written by Rosa Rowles
Sources
https://www.forbes.com/sites/stephenmcbride1/2020/05/14/why-the-largest-cyberattack-in-history-will-happen-within-six-months/?sh=62d5909d577c
https://www.fbi.gov/contact-us/field-offices/elpaso/news/press-releases/fbi-warns-public-of-virtual-kidnapping-extortion-calls
https://www.comparitech.com/identity-theft-protection/nigerian-scam/
https://www.social-engineer.org/framework/attack-vectors/vishing/
https://www.psychologytoday.com/us/blog/making-change/201307/dont-just-react-choose-your-response
https://www.humanhackingconference.com/
Image
https://www.infinumgrowth.com/four-human-emotions-6-ways-in-which-they-help-us-in-life/

