How can you protect yourself against common attacks?
How can you protect yourself against common attacks? First, it’s important to have a policy on how you want individuals to respond to suspicious activity; whether it’s suspicious activity on-site, over the phone, or on the computer. The next step is to make sure policies have been clearly communicated. It’s also important to reward employees who follow security policies and have a training plan for folks who fall short. Specific examples and ideas to protect yourself from common attacks are included below.
Vishing
One of the best ways to protect against vishing attacks is to have a way to confirm who you are speaking to. Best practice says no one should provide any information to an unknown caller without first verifying their identity. When in doubt, ask the caller for more information. If the caller cannot give you the information needed to verify themselves, or if the caller has a story as to why they can’t, it’s important to stick to policy. Inform the caller that you can not release the information until you are able to confirm their identity.
Ask for name, company, title, and phone number to call them back. In some cases, the malicious caller will disconnect when asked specific questions, especially if vague answers are met with a repeat of the question or if placed on hold. However, be aware that more advanced attackers will have a legitimate number to call back, so verification of that number may be a necessary step.
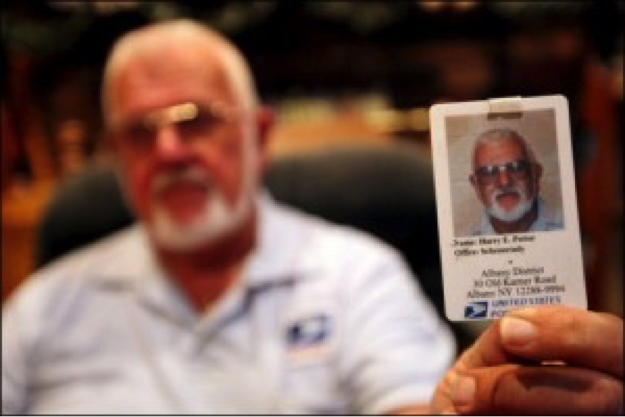
If the call appears to come from an internal source, it’s best to verify an employee ID before answering any questions. This is because malicious attackers use spoofing technology. All employees should be aware of what information tech support or HR can ask for over the phone. And how they will verify themselves.
Impersonation/Physical Attack
One important aspect of protection against impersonation attacks is an awareness of your surroundings. A clear understanding of who should be in the facility and the requirements for entry is critical. Attackers take advantage of fitting in and rely on the politeness or lack of attention of the target population.
Tech Support
One way to protect yourself against someone impersonating tech support in order to gain physical access to your computer is to know who your tech support person/company is and how to verify them as an employee. Have a policy in place and train employees on how and when to use it. It can be as simple as a two-sided badge with a verifiable ID number on the back of tech support badges, or as complicated as setting up a ticketing system for tech support visits.
Delivery Person
These attacks are hard to avoid. But with a security policy employees can stick to, and some practical training, this vector for attack can be controlled. One way to stop this attack is to limit the reception of deliveries to a secure reception area. Never allow delivery people to take items directly to a designated employee or area. If a delivery person must access your building, escort them to and from their destination and at no time leave them unattended. While, with proper planning, an attacker can fake an ID card, many will still not have the proper credentials to back it up. If you are still unsure if a person is who they say they are, call their company. The company will be able to tell you if they are in fact an employee and are scheduled to make a delivery.
USB Drops
There are a few ways to keep from falling victim to USB drops/plants. First, as stated previously, know how to verify a tech support person/company and if there is a policy that states whether or not tech support is allowed to use USB drives. Second, don’t use USB drives or CDs that are found anywhere in or around the office. Companies can allow employees to turn in USB drives found in or around the office to a specific location (usually in-house tech support if available). Businesses can also create a group policy to block recognition of USB drives on all corporate computers and then manage the settings to do so.
Phishing
The best way to protect against these types of scams is to not open emails that seem suspicious to you. Technical support will NEVER ask for your username and password since they can access this information if they need to (which they shouldn’t).
There are excellent phishing awareness programs available to educate users on the items to look for in a suspicious email (such as checking the spelling in URLs and hovering over links to see where they really go) and to test users on how well they spot a phish.
Conclusion
As you can see, there are many common social engineering attacks. However, by implementing security training and education, you can protect yourself from common attacks.