The Human Buffer Overflow
As security professionals we all love the idea of writing a good buffer overflow. To define, a buffer overflow is when extra data overwrites memory that may contain other data, including variables, instructions and program flow control. This can result in erratic behavior which can cause the program to terminate or give errors… or in security terms cause a breach resulting in code execution on the remote server. Now how can this be possible in the human brain? Can we get the human mind to “buffer overflow” and execute code we want it to?
A Simple Test
Lets establish a simplistic baseline for this discussion. Try to read the COLOR of the word not what the word spells. Do it as fast as possible, not stopping to think. It is not terrible, but it will illustrate how easy it is to inject a thought… if you succeed do it faster and faster if you can.
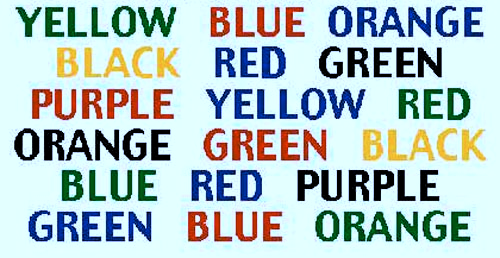
Why is this so hard? It is the way the human mind is wired. Our brain sees the color but it reacts to the word being spelled first. Therefore the thought in our minds is the WORD not the color. This exercise shows it is possible to have “code” execute in the human brain that might be the opposite of what the person is thinking or seeing.
Setting The Ground Rules
It has been proven that we speak 150 words per minute but we think at 500-600 words per minute. This means that most people we talk to can jump around our conversations in their heads. So overflowing the brain through fast speech seems almost impossible. We must also understand how people make decisions in life. Most decisions we make will be done subconsciously. We make decisions like how to drive to work, to get coffee, to brush our teeth, what clothes to wear without really thinking about it.
Have you ever driven all the way to work and when you get there, you can’t remember what billboards you passed, what route you took or that traffic accident on the news? You were in a state of mind that where your subconscious took over and did what you always do without consciously thinking about every turn.
Most decisions we make are like this. Some scientists even believe we make decisions up to 7 seconds in our subconscious before we make them in the real world. When we finally do make a decision consciously we do it from more than just what we hear… we get our sight, our feelings, yes, our emotions involved in the decision. Understanding how humans work and think can be the quickest way to creating our buffer overflow.
Fuzzing the HumanOS
Just like fuzzing a program, where we through different lengths and pieces of data at the program till it crashes, we have to understand how the human mind reacts to certain types of data. There are certain laws in the human mind that seem to be inherent and we all follow them. If you approach a building with two sets of doors and you hold the first set open for a complete stranger what do you think they will do next? Either hold the next set for you or make sure that set stays open till you get inside. Or if you are in a line of merging traffic and you let a complete stranger merge in front of you… most likely if you needed to merge later on he would let you in without even thinking. Why?
The Law of Expectations – The law of expectations basically states that a person will usually comply with an expectation. Decisions are usually made based on what that person feels the requester expects them to do. This is one way we can start sending our malicious “data” to the brain program… Presupposition.
Presupposition can be described best by giving an example:
“My next door neighbor Ralph always drives a green ford escort.”
In this sentence we presuppose:
- I know my neighbor
- His name is Ralph
- He has a license
- He drives a green car
To use presupposition effectively you ask a question using words, body language and facial expression that indicates what you are asking is already accepted. The basic gist of this is to bypass the “firewall” (the conscious mind”) and gain access directly to the root of the system (“the subconscious”). The quickest way to inject your own code is through embedded commands.
The Rules of Embedded Commands
There are some basic principles to embedded commands to make them work:
- Usually they are short – 3 to 4 words
- Slight emphasis is needed to make them effective
- Hiding them in normal sentences is the most effective use
- Our facial and body language must support the commands
Embedded commands are popular in marketing with things like “Buy Now”, “Act Now” and “Follow me” are common ones. Like any good shellcode we need some padding to help the commands find their way. We can utilize phrases that will help the target become padded to our code. Phrases like “When you…”,“How do you feel when you…”, “A person can…”, “As you…” – all of these statements create an emotion or a thought that allows you to inject code into the subconscious.
Let’s give an example… if you were on a sales call and wanted to use an embedded command you might say something like, “When you purchase a product like this from someone like me what features are most important to you?”
The bold letters are where emphasis is placed but the sentence causes the person to use their memory to think about a time they bought this product and what is really important, as that thought is occurring you are injecting your code “When you purchase from me…” What’s important is to not mess up our tones… if we are OVER emphasizing the words then we will sound odd and scare the person off instead of embed commands. Just like a normal buffer overflow the information must match the command we are trying to overflow.
Putting It All Together
As you probably have already imagined this is a vast field with a large room for messing up. Practice will be needed to be very successful at it. Although we do not promote using this information for seduction there are some decent videos that show how embedded commands can work.
We do not want to paint the picture that this becomes some Jedi mind trick. That is not the case. Just because you tell the person “You will purchase from me” does not mean they always will. So why use these commands? It creates a platform to make social engineering easier. It is also a good lesson to companies you work with to educate them what to look for and how to spot someone who may be trying to use this information against them.
Let’s Simplify
So let’s write out the equation more simply:
1. shellcode +=Law_of_Expectations
2. shellcode +=Mental_Padding
3. shellcode +=Embedded_Codes
Start off with phrases, body language and speech that is assumptive. Presume the things you ask for are already as good as accomplished.
Next pad the human mind with some statements that make it easier to embed code, at the same time embedding code. In essence this is the recipe for the human buffer overflow. Use it sparingly, but practice A LOT before you attempt it. Try it at work or home. Use simple exercises like trying to see if you can get a fellow employee to serve you coffee. “Tom, I see you are heading to the kitchen, will you get me a cup of coffee with 2 creams please?”
Escalate it to larger tasks to see how far you can get. Try to use this to get commitment from people. Eventually use this to see how much information you can get, how many commands you can inject. Let us know how it works for you.

