Technical Methods of Information Gathering
There are a variety of technical methods for information gathering. Some methods require high-tech equipment and in other situations low-tech options will work. No one source of information is the leading method to use. Nor is one method likely to give you enough data for the compromise. When preparing for a penetration test utilize multiple methods of gathering information and then synthesize the proper attack vector from that data.
Attackers also use these very same methods of information gathering to execute malicious social engineering attacks. This underscores the advisability of ongoing training and education of both top- level executives and employees.
Telephone
A phone call can capture the name and department of the person answering, basic lingo or protocols used by the organization, and more. After one phone call is completed, the pen tester can call back and use the information obtained previously to compromise the organization.
There are plenty of different ways to make the call. This may include burner cell phones, Google Voice, Skype, and other VoIP options. The Caller ID Spoofing section of the Framework has more details about these pen testing tools.
Online searches
Pen testers use search engines to find the following information:
- Corporate documents
- Resumes
- Floor plans
- Vendor relationships
- Phone numbers
- Job titles
- Email address protocol
- Business locations (even amazingly detailed photos of the buildings), and more.
A digital trip to the county auditor’s website provides a wealth of information. For example, the target building and property, as well as a listing of tenants within the building.
Corporate Websites
Corporate websites provide information regarding products and services, physical locations, job openings, contact numbers and biographies of the executives or board of directors. Support forums for products/services can be a gold-mine of information about policy, organizational jargon, or other data. Entities inside and outside the target may generate public data regarding an organization. This data may consist of quarterly, government, analyst reports, and earnings posted for publicly traded companies, etc.
Fingerprinting Servers
Fingerprinting servers for their operating system, application, and Internet protocol information can disclose a great deal of information about the organization’s infrastructure. Determining the platform and application in use can be combined with a search on the corporate domain name to find entries on public support forums. IP addresses may reveal if the servers are hosted locally or with a provider, and DNS records can reveal server names, functions, as well as IP’s.
User Sites
User sites such as blogs, and online videos may provide information about the target organization. In addition they also offer a more personal connection through the user(s) posting the content. A disgruntled employee that’s blogging about his company’s problems may be susceptible to a sympathetic ear from someone with similar opinions or problems. If the target’s industry is somewhat standardized than details such as jargon/vocabulary or policy can be gathered from industry or subject matter experts. And then applied to the specific target revealing possible vulnerabilities to social engineering.
There are a number of OSI (Open Source Information) or OSINT (Open Source Intelligence) training courses available that focus exclusively on this type of online information gathering.
Social Networking Sites
Searching social media accounts can reveal clues or possible answers to security questions, photos of employees wearing their ID badge, or linking a job title to a key individual’s hobbies/interests for phishing ideas. Try typing in a name of a coworker or friend and see how many hits or matches appear with their information.
Social media platforms such as Facebook, Twitter, LinkedIn help people connect. But, they also help pen testers find out about likes and dislikes, family, kids and hobbies. With this information, pen testers and malicious attackers can craft phishing emails or vishing calls with the right emotional triggers to successfully con their target. These social engineering tactics are highly psychological in practice.
Example
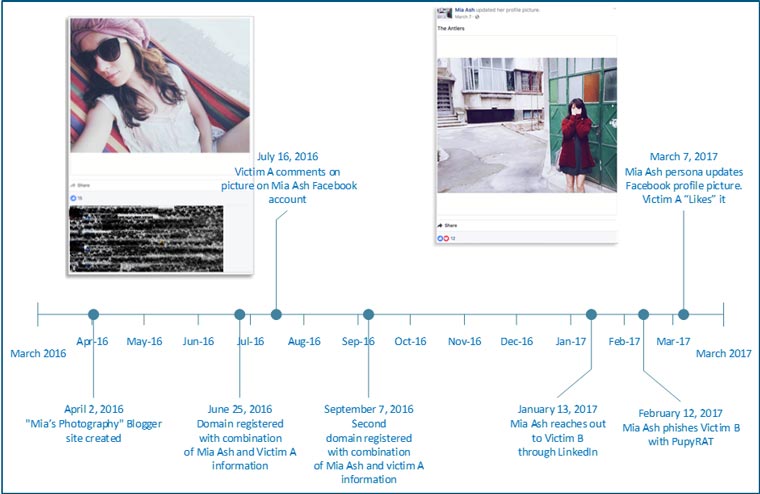
As reported by SecureWorks, ‘Mia Ash,’ a persona created by COBALT GYPSY/OilRig, used LinkedIn to search out an employee with a job title that implied administrative or elevated access to the corporate network. She then contacted the employee via the networking site with questions about photography. Mia and the employee messaged each other about their professions, photography and their travels. Mia then asked if he would add her as a Facebook friend so that they could continue their conversations there.
About a month later she asked him to participate in a photography survey. She then sent a Microsoft Excel document, “Copy of Photography Survey.xlsm” to his personal email account. Mia encouraged him to open the document using his corporate email account so that the survey could function properly. He complied; the attached survey contained macros that he enabled unleashing PupyRAT. The compromise of the individual was not the ultimate goal. But, rather served as the launch pad for breaching the target organization.
Social media is a technology that many companies have embraced. It’s cheap marketing that can reach a large number of potential customers. It’s also another stream of information from a company that can provide breadcrumbs of viable information.
Privately and publicly available search tools geared toward shifting through the metadata provided on social media sites are available. Please look at our Computer-based tools under the Social Engineering Tools section of the Framework.
Websites
According to Webroot Quarterly Threat Trends Report 1.4 million new phishing websites are created every month. Malicious attackers may include a link to a cloned site to collect employee credentials or other identifying information. A cloned website looks legitimately like the company it is impersonating, possibly a target’s own intranet site or a survey site that an employee would fill out. The employees answers can give either the pen tester, or malicious attacker the information they need to access the network.
Watering Holes
A Watering Hole attack is another example of using websites for information gathering, or compromise. In this attack, code on a legitimate website is compromised. As a result, whenever someone accesses that page their computer is infected with malware. This tactic is more likely to be seen “in the wild” rather than in pen testing. The attacker can pick a website that they think people in their target industry are likely to access then sit back like a lion waiting for a herd of zebra to visit the water hole. The attacker can pick a favorite target out of the herd that approached and mine that individual for information that will help complete the compromise.
Example
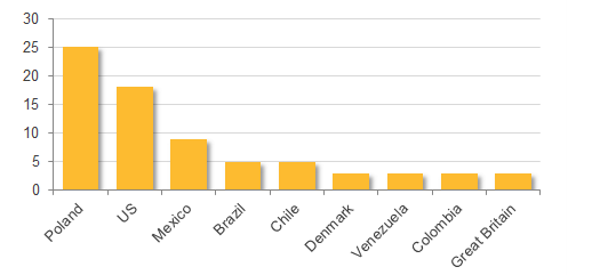
In February 2017, Symantec reported on a wave of watering hole attacks targeting 100 organizations in 31 different countries. Banks comprised the majority of targeted organizations with a small number of telecom and internet firms also on the list. The watering hole attacks have been traced back to the state sponsored hacking collective known as the Lazarus Group.
Conclusion
While no one source of information is likely to give you enough data for a compromise, social media platforms have emerged as the ‘go to’ resource for collecting personal and professional information. When used by malicious attackers the consequences can be devastating. Here are a few guidelines to help mitigate the risk.
1. Do not overexpose yourself or your organization on social media. Be security conscious when it comes to information you make public on any social media platform. Keep the privacy/security settings up-to-date on both personal and professional social media platforms.
2. Clear guidelines for social media usage, as well as education or identifying potential phishing lures are essential for all employees, including top level executives. Clear company policies should be in place for reporting potential phishing messages received through corporate email, personal email, and social media platforms.
For more information on technical tools of the trade, please see the Computer-based tools section of the Framework under Social Engineering Tools.

