Penetration Testers
NOTICE: The information in this article is for penetration testers to use during a professional pen testing audit ONLY and not for illegal purposes. Each reader will need to be aware of their locations and legal boundaries in regards to the tactics mentioned within.
Penetration testing (also called pen testing) is the practice of testing a computer system, network, web application or onsite perimeter to find vulnerabilities that a malicious attacker could exploit.
Penetration Testers and Social Engineering
Companies with authentication processes, firewalls, VPNs, and network monitoring software are still wide open to an attack if an employee unwittingly gives away key information. Social engineering is the human side of testing for corporate network vulnerabilities. Penetration testers employ multiple tactics to test their targets. By means of phishing, vishing, and impersonation a pen tester will mimic attacks that a malicious social engineer would use to attempt a system breach. Depending on the scope of work, penetration testers may also seek employment at the target company. The sole objective while employed for the target company is to maintain their pretext and elicit information.
According to the 2022 Verizon Data Breach Investigations Report, 82% of breaches involved the human element. Whether it is the use of stolen credentials, phishing, misuse, or simply an error. This statistic underscores the value of incorporating “the human side” in penetration testing.
Penetration Testers and Phishing
Penetration testers (or pen testers), primarily use phishing for three different purposes. First, as part of a pen test which usually leads to a controlled compromise of the organization’s digital or human network. Exposed vulnerabilities are reported in detail to allow the organization to strengthen their security. Second, as part of a security awareness program throughout the year that focuses on educating users on the different levels of phishing. Third, to set a baseline for assessing user susceptibility to phishing attacks and to justify future training on the topic.
Preparation
For the pen tester, thorough internet “snooping” is indispensable. The most innocuous information can be useful in a potential pen test. By utilizing social media profiles such as Facebook, LinkedIn, and Twitter, you can learn a great deal about likes, dislikes, interests and family connections. With such information the pen tester can craft an email that appeals specifically to the individual. Subject lines that include messages such as “error”, “account closed”, or “warning” urge the recipient to act before thinking.
The Value of Pen Testing and Phishing
Many companies will spend thousands of dollars on IDS systems, firewalls and other protection devices to monitor the network. However, all it takes is one phishing attack to potentially devastate a company.
Example
In March, 2017, Barricuda released a report on a phishing email targeting corporate travelers that had a 90% success rate. As reported by Barracuda, these phishing emails were well-researched and specifically prepared for the target. For example, the airline, destination, and price looked legitimate in the context of the company and the recipient. There are two variants to the attacks — one type drops data-stealing malware. The second type attempts to steal credentials by including links to a phishing website designed to imitate an airline website or the expense/travel system used by the targeted company. With the stolen credentials the attacker will then try to infiltrate the corporate network and internal company systems.
Penetration Testers and Vishing
Vishing also commonly known as voice phishing or phone elicitation, is a rapidly growing social engineering attack vector.
Pen testers primarily use vishing for the following purposes. First, simulated attacks are an effective way to assess vulnerabilities. Second, extensive reporting provides actionable data about employee responses to various vishing attack scenarios. Third, ability to identify which departments or employees are most susceptible. Fourth, based on results from vishing assessment, develop a continuous assessment and training process to successfully combat vishing attacks.
Preparation
Equipment Needed For Vishing
1. Phone Line. – Land line, cellular phone, burner phone, VoIP (internet phone)
2. Spoofing technology – software, service or self served.
3. Pretext – Know whom you are impersonating so well that you are comfortable conversing and answering questions.
4. Flag/goals– Know what information you need to obtain and the questions you can ask to elicit that information.
Security Consultants, Chris Hadnagy, CEO of Social-Engineer, LLC and Michele Fincher, demonstrate this attack vector at DEF CON 24.
The Value of Pentesting and Vishing
Vishing attempts are difficult to monitor and trace, and attackers are increasingly leveraging this mechanism to extract information and compromise organizations. Employees in customer service, sales and HR departments are highly vulnerable to these types of attacks. Security audits that include simulated attacks are an effective way to assess vulnerabilities. However, the best way to ensure lasting behavior change is to teach employees how to identify and respond to vishing threats. All it takes is one vishing attack to potentially devastate a company.
Example
In August, 2017, The Boulder Valley School District found themselves the victims of a vishing scam that stole $850,000 in bond construction money. Equipped with publicly available information regarding contracts between the school district and Adolfson and Peterson Construction Company; the attacker called the school districts’ accounts payable department pretexting as an employee of the construction company. The attacker requested that the school district change the way Adolfoson and Peterson was paid. The accounts payable department complied with the request, and began sending payments to a fraudulent bank account. The school district did not become aware of the theft until they started to receive late payment notices from the genuine Adolfson and Peterson Construction Company. The Boulder Valley School District has since added safeguards after falling victim to this devastating vishing scam.
Penetration Testers and Impersonation
The impersonation of a delivery person is an effective vector for a pen tester to utilize for two basic reasons. First, the pentester does not need much acting experience. Second, wearing a uniform or some type of company logo engenders trust. If a company hires you to conduct a security audit and you need to get equipment into a building, such as a jail broken iPod, it’s one of the best ways to accomplish this.
Example
Job Seeker Impersonates Postmates Delivery Person
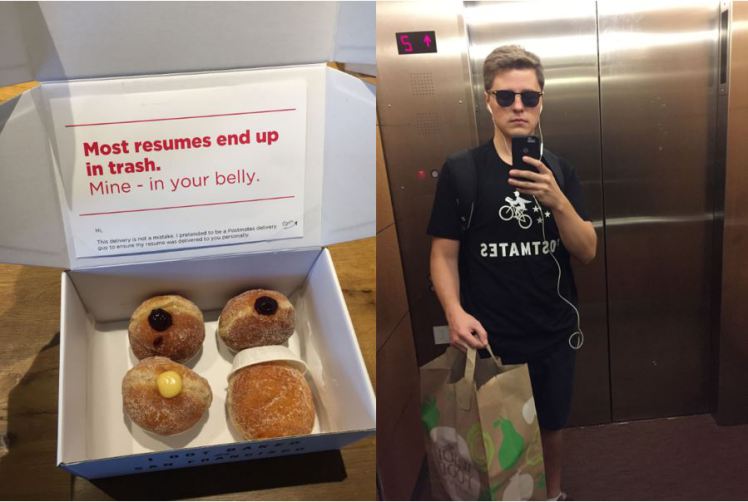
Although there was no malicious intent with this impersonation, it illustrates how easy it is to gain entry, simply by looking the part.
Preparation
A few things need to be in place first to effectively impersonate a delivery person. First, be aware of which delivery firms the company uses and their route times. Nothing could thwart your pentesting engagement more than entering your targeted building dressed as a delivery worker only to be greeted by the person who is actually doing the job. Second, it’s important to look the part. Are you planning to impersonate the local flower or pizza delivery person? Research is necessary to find out if a standard uniform is worn or not. Will you be impersonating FedEx, UPS, a mail courier or bicycle messenger? Then wearing the correct uniform and having the appropriate ID is vital.
How To Buy
UPS and FedEx uniforms can be found online at either Ebay or Craigslist. Due to the rise in crimes committing while impersonating delivery people/companies it is getting harder to locate these uniforms. Another option is to purchase an appropriate colored plain shirt and print the desired delivery company logo on it. A silk screen company might be willing to do the printing, however since the end use is for a pen testing engagement and not for legitimate business, this option is not recommended. A last option is to check out thrift stores for used shirts and uniforms.
Important Note:
Impersonating a United States Postal Servant is illegal. According to Title 18 US Code sec. 912, “Whoever falsely assumes or pretends to be an officer or employee acting under the authority of the United States or any department, agency or officer thereof, and acts as such, or in such pretended character demands or obtains any money, paper, document, or thing of value, shall be fined under this title or imprisoned not more than three years, or both.”
Because USPS impersonation is illegal, a professional pen tester should never use this vector.

