Impersonation
At Social-Engineer, we define impersonation as the “practice of pretexting as another person with the goal of obtaining information or access to a person, company, or computer system.”
Impersonation scams can be carried out via social media platforms, phone, or even email. However, in this Framework Page we are focusing on physical impersonation attacks with the intent to gain physical intrusion.
NOTICE: Never use this information to perform illegal acts! The purpose of the Social Engineering Framework is to help ethical social engineers learn the skills they need in their adversarial simulation jobs. We also discuss these details to educate organizations about possible social engineering attacks. This will help organizations decide which services may help them defend against these attacks.
Technical Support Impersonation
A bad actor impersonating as a tech-support worker can have devastating effects on a network. This is because it gives the attacker physical access to network computers. In a matter of seconds, a bad actor can compromise a computer using a USB thumb-drive. Thumb-drives are small, easy to conceal, and can be loaded with different payloads depending on what task needs to be done. For example, and attacker may claim that they have “helpful” files to download, such as an “anti-virus” program or some sort of scanner to “clean” the computer. However far from being helpful, these files are malicious, creating an opportunity for the bad actor to infect the computer. Once the computer is infected the criminal can now gain further access to other computers, or to the network.
Criminals may also employ a USB drop attack. In the drop attack, a bad actor purposely leaves USB thumb-drives containing malicious software in a public place and waits. The bad actor is hoping that an employee will pick up the USB thumb-drive and insert it into their computer to identify its contents and owner. If an employee inserts the infected USB thumb-drive, the malicious software either executes automatically, or with the user taking some action.
Vendor Impersonation
Impersonating as a known vendor is a common ruse threat actors may use to penetrate a building. Conducting OSINT (Open-Source Intelligence) on the target company can reveal who their current vendors are. Possible vendors may include:
-
-
- Pest Control
- Office Equipment Technician
- Vending Machine Supplier
- Office Supply Delivery
-
The most challenging element to this attack is looking the part and having the correct credentials and papers in order.
Example: Posing as Ortho Pest Control
In December 2016, a man wearing a hazmat suit and carrying an ‘Ortho’ identification card signs in at the security desk of a commercial building. A guard later found him on the third floor of the building disconnecting a laptop computer.

Delivery Person Impersonation
A bad actor may choose to impersonate delivery people because it’s an easy attack that requires little acting. For example, bad actors may impersonate local food or flower delivery services, bicycle messengers, or couriers. Many times, these delivery people and messengers will be let right into a building.
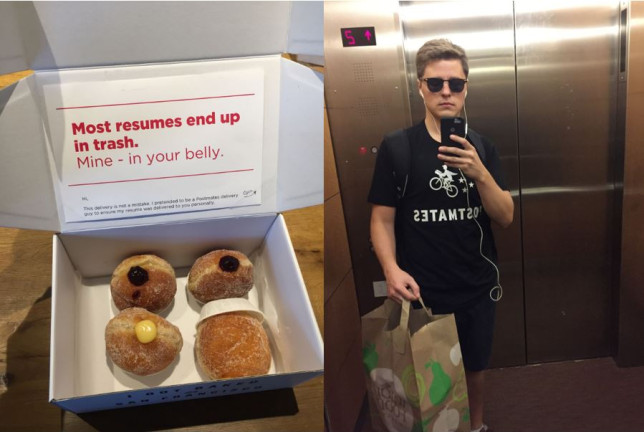
Example: Posing as a Postmates Delivery Person
In October 2016, Lukas Yla, posing as a Postmates delivery person, infiltrated some of the largest Bay Area tech and advertising companies delivering donuts. Yla’s intent was not malicious, he just wanted to hand deliver his résume in an unforgettable manner. What made Yla’s impersonation so credible? First, he did research. He started by finding the best donuts in the area. Then, he ordered lunch from Postmates to see how they did delivery. Next, he designed a T-shirt that copied the Postmates logo and found a printing company willing to make the T-shirts. Finally, he hand-delivered donuts and his résume to top executives. How did the executives respond? Yla reports that most were shocked, wondering how he got into the building.
Although there was no malicious intent with this impersonation, it illustrates how easy it is to gain entry to buildings simply by looking the part.
Protect Your Organization
To protect your organization against impersonation attacks, it’s important to empower your employees to act on perceived “stranger danger.” Since it’s not always possible to memorize the faces of known vendors or delivery people, having policies for dealing with unknown personnel identification and access is vital to protect your organization. For example, your employees should be encouraged, even expected to question people they are suspicious of. And they should feel confident that if they become suspicious of an unknown person and respond according to company policies there will be no repercussions if the suspicious person is indeed legitimate.
Example: Dr. Straface—Alert to Stranger Danger
Dr. Samuel Straface, CEO (Chief Executive Officer) of Medrobotics has a personal policy; if he doesn’t recognize you, then you have earned an introduction. Because he is alert for unfamiliar faces, Dr. Straface, discovered a physical intruder and protected his company’s trade secrets. You can read about it in the Resources Section of Social-Engineer, LLC.
Why Adversarial Simulators Use Impersonation in Security Audits
With good planning, bad actors can gain physical access to restricted areas of your company. In view of this, it’s vital to test your organization’s human network. For example, the Social Engineering Teaming Service includes an impersonation component. During this component, professional social engineers try to gain physical access to restricted areas of your company. They may do this by impersonating a vendor, a delivery person, an employee, contractor, or person of authority. This is an important aspect of security training because it assesses employee understanding of policies regarding visitors and unknown personnel identification and access. It also assesses employee adherence to policies related to unknown or discovered USB keys and other media or network connected devices.
Are you wondering what an impersonation component is like? Read more about it on the Resources Section of Social-Engineer, LLC.
NOTICE: It is illegal to impersonate government employees, such as USPS carriers, so reputable adversarial simulators will not use this attack method.

