Delivery Person
The impersonation of a delivery person is a powerful weapon in a criminal’s arsenal, because it does not require much acting. Usually, the most difficult thing about impersonation is looking the part, and having the necessary credentials, papers, and “deliveries” in order.
Impersonating a Delivery Person
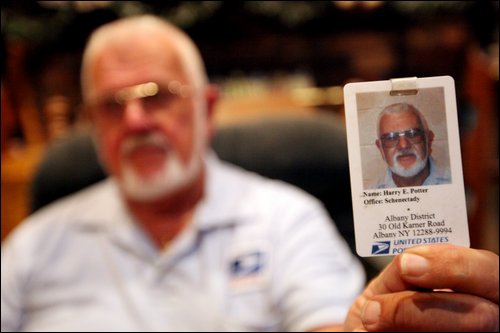
A criminal may choose to impersonate a USPS mail carrier because people trust the uniform. Indeed, a USPS mail carrier can typically walk in and out of buildings with few restrictions. They may even get access to secure areas to deliver packages with little or no questions.
The flower or pizza delivery person will not necessarily have a standard uniform, making impersonation easy to perpetrate in a social engineering attack. In larger cities, bicycle messengers or couriers are a common service. Often these messengers have access to buildings. And, while the receptionist is busy confirming the order/delivery; the attacker might seek access to a computer to plant a malicious USB key.
NOTICE:
Impersonating a United States Postal Servant is illegal. According to Title 18 US Code sec. 912, “Whoever falsely assumes or pretends to be an officer or employee acting under the authority of the United States or any department, agency or officer thereof, and acts as such, or in such pretended character demands or obtains any money, paper, document, or thing of value, shall be fined under this title or imprisoned not more than three years, or both.”
Because USPS impersonation is illegal, a professional pen tester should never use this vector.
Examples of Impersonation
In December 2016, a man wearing a hazmat suit and carrying an ‘Ortho’ identification card signs in at the security desk of a commercial building. A guard later found him on the third floor of the building disconnecting a laptop computer. The investigation is ongoing.
An Alabama man is captured on surveillance posing as a delivery man and casually loading up carts of beer and soda. In fact, multiple stores in the Prattville, Alabama area have fallen victim to his impersonation.
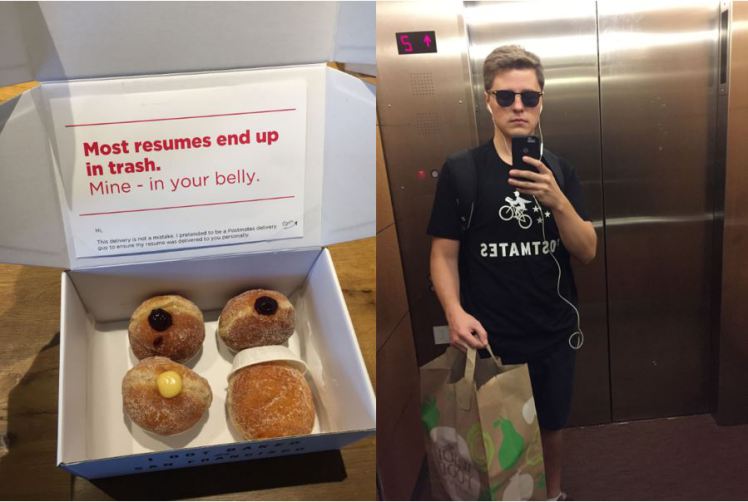
In October 2016, Lukas Yla, posing as a Postmates delivery person, infiltrated some of the largest Bay Area tech and advertising companies Although there was no malicious intent with this impersonation, it illustrates how easy it is to gain entry to buildings, simply by looking the part.
Wearing a hardhat and t-shirt a man posing as a construction worker walks off with $15,000 in laptop computers.
How Can You Protect Your Organization?
With education and training these attacks can be avoided. Indeed, one of the best ways to protect your organization is to know who your regular delivery person is. Typically, it will be the same person for a given area. If it is not your regular delivery person, ask for credentials. For USPS employees, they must carry identification with them. Keep in mind though, that with proper planning, an attacker can even fake an identification card.
The best way to prevent this attack from happening is to not allow a delivery person past the front desk unattended. If a delivery person must enter your building, escort them, and do not leave them alone. This will mitigate the chances they have for an attack. If you are still unsure if a person is who they say they are, call the company they work for. The company will be able to tell you if they are in fact an employee.
Impersonation and Pentesting
To see how impersonation is used in a professional pentesting engagement, please see this article.

