Dumpster Diving
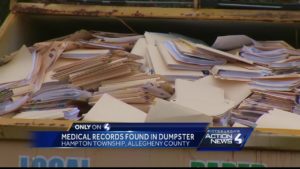
What can you find in a dumpster besides trash? While dumpster diving, you may find medical records, resumes, personal photos, emails, bank statements, account details, information about software, tech support logs, and so much more. For instance, this article reports on medical records found in a dumpster.
Dumpster Divers
Dumpster divers are diverse people. There are those searching for food or clothing. Others are looking for information to commit identity theft. Security professionals practice dumpster diving as part of their security services. This article we found at About.com explains some of the dangers of people sifting through company trash.
Legality
In the USA it is not illegal to take things that are put in the trash. However, there is a large caveat to this. If a dumpster is on private property, then it may be considered trespassing to go on their property and enter their dumpster. For more information regarding the legality of dumpster diving see this article, California vs Greenwood.
Why Does Dumpster Diving Work?
As with most forms of social engineering, “Working smarter, not harder” is a good slogan. Doing hours of work brute-forcing a password or account number may be unnecessary when you can just obtain the same information from something as simple as a discarded and unshredded post-it note.
Information Diving
The more common form of dumpster diving, as it pertains to hacking and identity thieves is Information Diving. An attacker may use innocent looking information like a phone list, calendar, or organizational chart to gain access to the network. Benjamin Pell is a famous British dumpster diver who has made a living of selling off his “prizes”.
Crime and Clues
Dumpsters: Beware of the Treasures. The website Crime and Clues has a nice article we archived here. This article shows how people discard valuable information because they do not think someone would dig through their trash to get it.
No Tech Hacking
One of the best resources we could find on dumpster diving for the field of security is Johnny Long’s book “No Tech Hacking”. This books is full of amazing information regarding Social Engineering. Page two starts an Introduction to Dumpster Diving.
Tiger Team
A team of social engineers in one episode of Tiger Team show how they use a bag of trash to find valuable details about their target. In the trash they found the name of the tech support team. Then, they where able to send in a team member to act as a support employee and was given full access to their servers.
Original source: YouTube.

